We received the below from Garmin and thought it important enough to pass on:
*** Warning Garmin Customers: Cyber-Fraud Alert ***
Garmin has been made aware that there are attempts being made to mislead Garmin customers into making payments to cyber-criminals pretending to be Garmin via realistic looking emails. We would like to provide the following tips to help prevent you and Garmin from falling victim to this type of cyber-fraud.
Garmin’s Standard Accounts Receivable Processes
Garmin will only send wire transfer/ACH information via ENCRYPTED email
Garmin would NEVER change our banking information without significant communication, both before and after
In addition, we recommend that:
You ALWAYS reach out to your vendor, via known communication channels, before changing any payment information
You are careful transacting via email; email addresses can be spoofed, misleading, or compromised (see below)
How can you tell if an email is fraudulent?
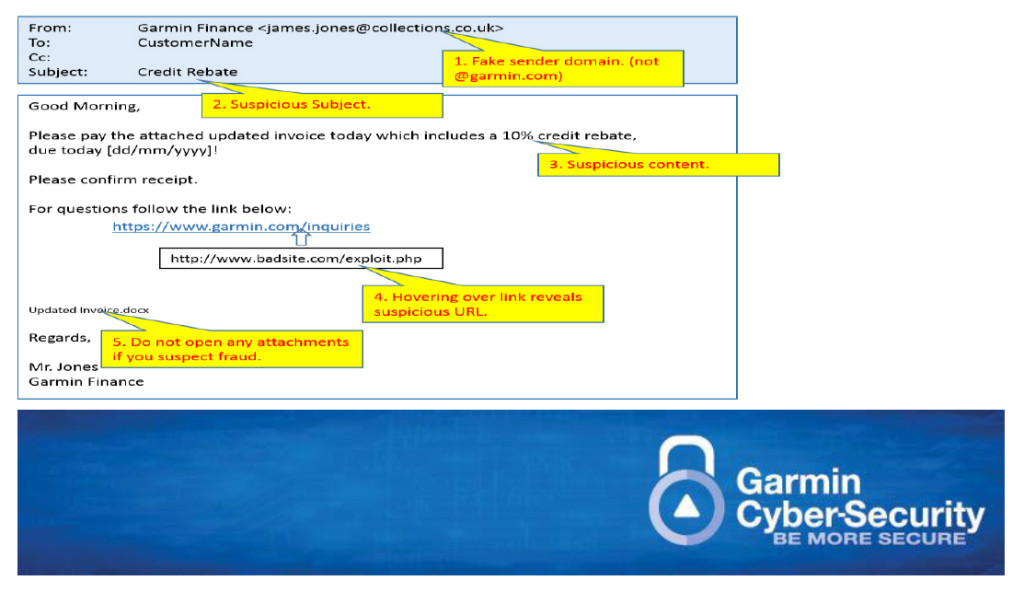
Look closely at the sender’s email address (“From”). The email may appear to come from Garmin but the actual address is not garmin.com although it may closely resemble a valid address. Fraudulent examples: Garmin Accounts Receivable <jane.smith@garm1n.com>; Garmin Finance <james.jones@collections.co.uk>, Garmin Order Management <marco.polo@gmail.de>.
If there are any links, hover or place your computer mouse pointer over the link to reveal its true associated Web URL. If the true destination is different than what is shown in the email, this is an indication of fraud.
DO NOT open any attachments if you suspect fraud.
What to do if you’ve responded to a fraudulent email?
Sent payment? – Contact your financial institution immediately to stop payment. Report to your local authorities. Inform your Garmin representative.
Clicked on a link or opened an attachment? – Follow your internal security incident procedures.
What to do if you suspect an email is fraudulent?
Contact your Garmin representative. If determined to be fraud, report to your local authorities and follow your internal security incident procedures.